Hackers Have Infiltrated Tor Browser And It Cannot Get Eliminate Them.
A mysterious cluster of hackers has hooked up many malicious servers to the network of privacy-focused browser Tor, that are being employed to execute targeted attacks on users.The Tor operators are wrestling with the hackers since January, per a report from freelance security investigator Nusenu, U
The servers that bridge the network with the general public internet.
A mysterious cluster of hackers has hooked up many malicious servers to the network of privacy-focused browser Tor, that are being employed to execute targeted attacks on users.
The Tor operators are wrestling with the hackers since January, per a report from freelance security investigator Nusenu, UN agency has monitored the network for a variety of years.
At the height of the attack in could, the hackers operated a complete of 380 Tor exit relays the servers that bridge the network with the general public internet, which means every user had a roughly one in four likelihood of being funnelled through a dangerous server.
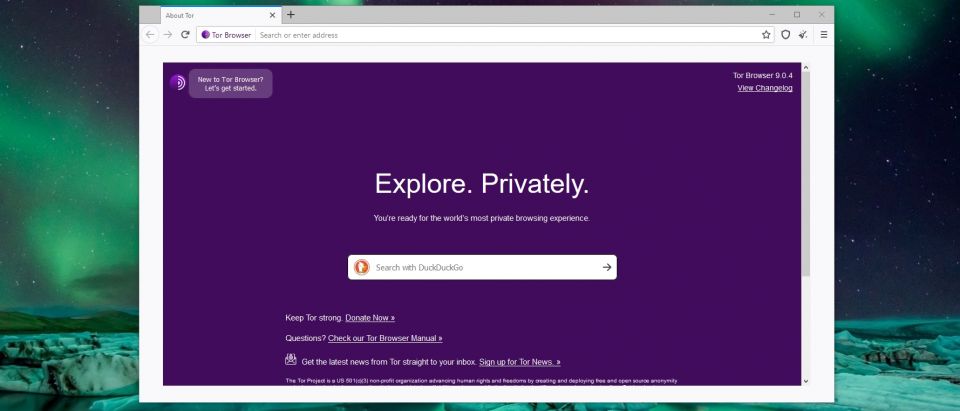
Having gained a robust foothold within the Tor network - that is sometimes thought of among the foremost secure around - the hackers have launched targeted attacks against users of cryptocurrency websites.
“They perform person-in-the-middle attacks on Tor users by manipulating traffic because it flows through their exit relays,” wrote Nusenu. “They (selectively) take away HTPP-to-HTTPS redirects to realize full access to plain unencrypted protocol traffic while not inflicting TLS certificate warnings.”
This sort of attack is understood as SSL husking and permits malicious actors to take advantage of the actual fact users seldom type out full web site URLs (including https://). during this context, the hacker's ar exploitation the exploit to switch bitcoin addresses in unsecured protocol traffic and funnel cryptocurrency payments into their own wallets.
Tor Browser reportedly lacks the flexibility to verify new relay operators at a sufficient scale, which means there's no immediate resolution in view. However, Nusenu claims to own contacted the cryptocurrency websites wont to execute the hijacking attacks, that might value more highly to implement countermeasures.
Disclaimer: The opinions expressed within this article are the personal opinions of the author. The facts and opinions appearing in the article do not reflect the views of 25hrNews and 25hrNews does not assume any responsibility or liability for the same.





 (+91) 8081113111
(+91) 8081113111 pr@25hrnews.com
pr@25hrnews.com